autoupdater and connection temp.sh
-
@PeterJones
Notepad++ v8.8.4 (64-bit)
Build time: Aug 4 2025 - 18:01:28
Scintilla/Lexilla included: 5.5.7/5.4.5
Boost Regex included: 1_85
Path: C:\Program Files\Notepad++\notepad++.exe
Command Line:
Admin mode: OFF
Local Conf mode: OFF
Cloud Config: OFF
Periodic Backup: ON
Placeholders: OFF
Scintilla Rendering Mode: SC_TECHNOLOGY_DIRECTWRITE (1)
Multi-instance Mode: monoInst
asNotepad: OFF
File Status Auto-Detection: cdEnabledNew (for current file/tab only)
Dark Mode: OFF
Display Info:
primary monitor: 1920x1080, scaling 100%
visible monitors count: 3
installed Display Class adapters:
0000: Description - Intel® Iris® Xe Graphics
0000: DriverVersion - 32.0.101.6556
0001: Description - DisplayLink USB Device
0001: DriverVersion - 12.1.2424.0
0002: Description - DisplayLink USB Device
0002: DriverVersion - 12.1.2424.0
OS Name: Windows 11 Pro (64-bit)
OS Version: 24H2
OS Build: 26100.6584
Current ANSI codepage: 1252
Plugins:
ColumnsPlusPlus (1.1.2)
CSVLint (0.4.6.7)
JsonTools (8)
mimeTools (3.1)
NppConverter (4.6)
NppExport (0.4)
XMLTools (3.1.1.13) -
@PeterJones
gup.exe : 807,936 byes, created Sunday, August 10, 2025
libcurl.dll : 818,688 bytes, created Sunday, August 10, 2025
notepad++.exe : 8,699,392 bytes , created Sunday, August 10, 2025 -
@soft-parsley said,
Notepad++ v8.8.4 (64-bit)
Build time: Aug 4 2025 - 18:01:28and
gup.exe : 807,936 byes, created Sunday, August 10, 2025
libcurl.dll : 818,688 bytes, created Sunday, August 10, 2025
notepad++.exe : 8,699,392 bytes , created Sunday, August 10, 2025Hmm… Those all match with what I see for a correct Notepad++ v8.8.4.
I don’t know why you would see
curl.exerather thancurl.dll, or the strange URL and AutoUpdater.exe, because I really wouldn’t expect that as normal behavior. I think you’re going to have to wait for @xomx or someone else more knowledgable than I am about the updater process, because the files look right to me, but the activities seem weird, to me. -
Unfortunately, I’ve a bad news for you, if you didn’t somehow initialize all of this yourself, your comp is no longer yours…
t e m p . s h seems to be a kind of non-permanent storage, anyone can use it:
Notepad++ doesn’t distribute/use
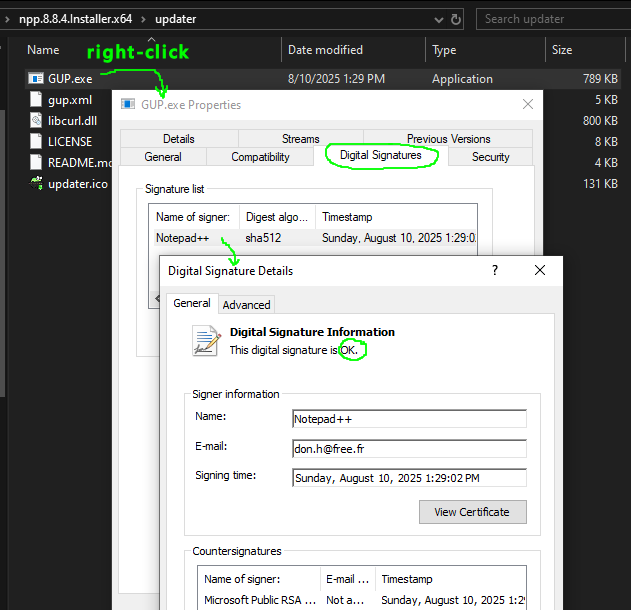
curl.exebinary, it uses the curl-library functionality via “C:\Program Files\Notepad++\updater\libcurl.dll” for the N++ updater GUP.exe. And of course N++ never uses such an anonymous storage place.Also you should check the digital signatures of your N++ binaries like:
Moreover, nowadays it isn’t possible to download or update to N++ v8.8.4, as this specific version was withdrawn because it contained regressions.
-
@soft-parsley
Could you provide yourgup.xmlfile fromC:\Program Files\Notepad++\updater\directory? -
@donho I see in v8.8.8 release there was an issue addressed with WinGup. Could you elaborate what caused this behavior?
-
I see in v8.8.8 release there was an issue addressed with WinGup. Could you elaborate what caused this behavior?
Unfortunately I can’t provide more facts than what we already know.
We are not aware of any confirmed exploitation of this vulnerability in the wild.
The fix in v8.8.8 is the best I could do to address the issue of WinGUp being hijacked. -
Thank you for all the work you do, I’m a huge fan of Notepad++, I wanted to confirm a few details due to the heavy usage of Notepad++ in my environment:
Regarding the WinGup fix in v8.8.8, Was the
temp.sh(or similar) exfiltration vector reported in v8.8.4 possible on a clean, official installation of Notepad++?Was administrative privileges on the Windows computer where 8.8.4 is install required to exploit the vulnerability?
You mentioned the fix landed in v8.8.8, but can you confirm if this vulnerability was introduced specifically in v8.8.4 (due to changes in the updater), or were versions prior to 8.8.4 (like 8.8.2/8.8.3) also susceptible to this specific gup.exe hijacking technique? What about 8.8.5-8.8.7?
For users currently running v8.8.4 who want to verify they haven’t been impacted before updating: Aside from monitoring network traffic for
temp.sh, are there specific things we can check for, like modifications to the update xml file or other modified files/logs in the program directory? -
From what I know, this is not directly about a bug/vulnerability in the N++ ecosystem, but rather a preventive security fortification against possible attacks independent of the N++. Namely against the DNS spoofing type of attacks. The upcoming v8.8.9 will bring another such fortification.
-
@SammyBolt said in autoupdater and connection temp.sh:
Regarding the WinGup fix in v8.8.8, Was the temp.sh (or similar) exfiltration vector reported in v8.8.4 possible on a clean, official installation of Notepad++?
The temporary fix prevents the hijacking attempts that redirect to the domain other than github.com. However, it cannot protect against malware that is hosted on github.com.
The full fix will be included in the upcoming version, as mentioned below.
You mentioned the fix landed in v8.8.8, but can you confirm if this vulnerability was introduced specifically in v8.8.4 (due to changes in the updater), or were versions prior to 8.8.4 (like 8.8.2/8.8.3) also susceptible to this specific gup.exe hijacking technique? What about 8.8.5-8.8.7?
We still cannot determine the exact method used by the attacker. But it is not a case of “a vulnerability introduced in version X”.
For users currently running v8.8.4 who want to verify they haven’t been impacted before updating: Aside from monitoring network traffic for temp.sh, are there specific things we can check for, like modifications to the update xml file or other modified files/logs in the program directory?
I do not have complete information to provide specific advice. However, here’s an article from a security expert who appears to have investigated this issue:
https://doublepulsar.com/small-numbers-of-notepad-users-reporting-security-woes-371d7a3fd2d9My suggestion is download & install v8.8.8 manually from the official website.
The upcoming release v8.8.9 will be available in a few days. In this release the code signing certificates will be verified on the downloaded binary before update installation.
Then please update to v8.8.9, in which the vulnerability is fully addressed. -
FYI:
Security Update - Resolution of Notepad++ Update Server Compromise
https://notepad-plus-plus.org/news/hijacked-incident-info-update/ -
Seeing reactions all over the net to this attack, I’d like to try to clear some of the frequently asked questions: “Was my PC vulnerable/attacked/compromised too?” usually followed by “What should I do now?”. And also the common “Is this a Notepad++ fault or what?”. And remember, all the following is my personal view only. Also don’t ask me please for more attack details, the investigation is still ongoing and @donho will surely disclose more whenever/if it’ll be possible to do so.
Before I try to answer these questions, I have to explain 1st a little the N++ auto-update mechanism, as with every successful attack the attackers searched & found a weak-spot and this time it was the N++ automatic updates mechanism.
N++ auto-update simply works as:
- you installed a N++ version X.Y.Z, date of that installation is stored into a N++ config file
- when that installed N++ app is launched after a predefined period of time (I think, the default is 14 days), it issues a net-request to the N++ (compromised) server about a possible newer version than the current X.Y.Z and gets a response (yes/no, together with a link to the possible new updated binaries/installer)
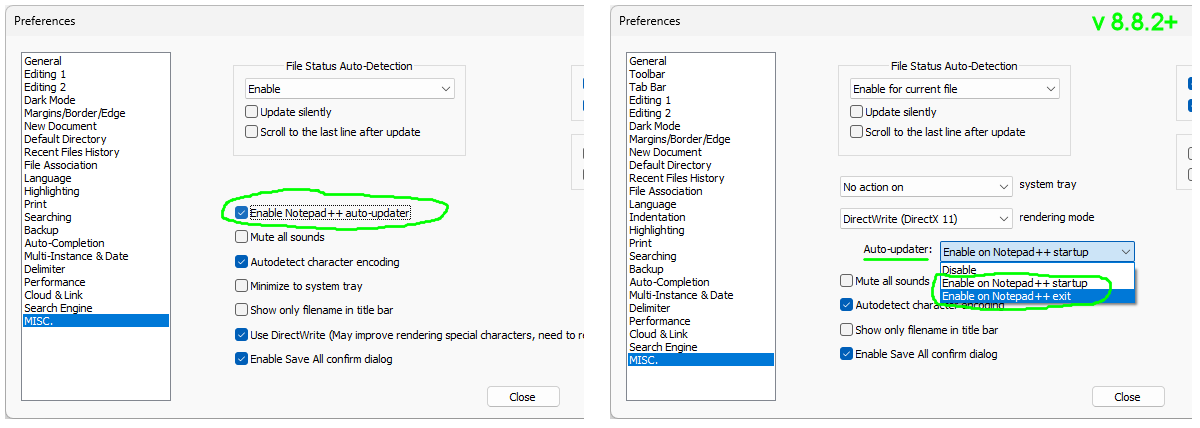
- then the app is being updated (at exit or start of the N++ app, see the setting pics below)
More about that stuff e.g. here: https://github.com/notepad-plus-plus/notepad-plus-plus/issues/16759#issuecomment-3016024980
Now you can see the weakness, as the attackers were able to hack the N++ hosting provider server, they were also able to intercept/change the N++ updater answers from the PHP script running there and redirect these answers for specific IP addresses they were interested in.
Now to the questions:
-
Was my PC vulnerable too?
Only the users with this N++ setting ON could be affected:
and only if there was at least one real N++ version auto-update in the attack-window (Jun 2025 - 2nd of Dec 2025, which means N++ updates to v8.8.2 - v8.8.8). Note that N++ binaries (installers and portable archives) have not been compromised at all, they reside at the GitHub https://github.com/notepad-plus-plus/notepad-plus-plus/releases/ -
Was my PC attacked too?
Most probably not. This was a highly targeted “supply chain” type of attack against some East Asia orgs. -
Was/is my PC compromised too? What should I do now?
The attackers attack was to collect/steal info one, so not a crypto-virus etc. (spreading and infecting your other files). But if you are in the theoretically affected group of users (see above), I’d highly recommend:
- full AV scan of your PC (if you don’t have any, you can e.g. use this offline MBAM: https://downloads.malwarebytes.com/file/mb5_offline )
- manual re-installation to the latest Notepad++ v8.9.1
- changing/rotating all your passwords used in that attack-window on/from your PC
- Is this a Notepad++ fault or what?
Yes, definitely. I’m saying this even if the attack target was not primarily the N++ app-code but an external hosting server. Once that server had been compromised (well, this itself was not a N++ fault), attackers could attack the N++'s distribution network/mechanism without further obstacles, which is just wrong (nowadays).
All I can say to defend N++ here is that it’s always easy to be wise after something…
Unfortunately, in the future, it’ll be necessary to devote the precious time of active contributors to the N++ project, instead to the app’s own functionality, also more to its security. So, at this point, I’d like to invite any of you using the N++ who are good at security, to also contribute a little of your experience and time for keeping this app up-to-date from a security POV. It’s opensource SW folks, not a magic box programming and maintaining itself.
-
Addendum to the points 2. & 3. above - even if you’re not to Reverse Engineering much, just follow the link and skip it to the ending “Indicators of compromise” part, where are some common markers that could help you decide whether or not your comp has been compromised:
https://www.rapid7.com/blog/post/tr-chrysalis-backdoor-dive-into-lotus-blossoms-toolkit/
-
@xomx said in autoupdater and connection temp.sh:
I’d like to invite any of you using the N++ who are good at security, to also contribute a little of your experience and time for keeping this app up-to-date from a security POV.
A great idea, if late in coming. But I also can’t deny the truth of this hot take from a reader of The Register’s article about this event:
[U]ltimately it’s Microsoft who caused this by deciding to have an ecosystem where securely distributing your software costs $300 per year
I would even suggest — if you want to do the most good with your contribution — give it to a project involved in bringing the Notepad++ experience to other platforms (via Qt 6, e.g.,NotepadNext) or even MacOS.
Windows was never a suitable environment for open source, and even its historically dominant user base will shrink as more and more people realize they cannot safely do personal computing on a device with AI surveillance permanently baked-in to the operating system.
-
@xomx Really appreciate you leaving this reply.
Could I just double check something to put my mind at ease:
I installed notepad++ on a new machine in mid november (listed build time nov 16, installed nov 25 from a github sourced exe), so version 8.8.8. Am I understanding things correctly that this should basically put me in the clear?
As the update feature from that version onwards, no longer pointed to the compromised domain. And as such if you have 8.8.8 installed, the only way for it to be compromised is if it was automatically updated from an older version, rather than installed directly?
Thanks again.
-
As the update feature from that version onwards, no longer pointed to the compromised domain. And as such if you have 8.8.8 installed, the only way for it to be compromised is if it was automatically updated from an older version, rather than installed directly?
If you have 8.8.8 installed and if you update to the new version manually, you’re not concerned by this incident.
The current state is, with the new hosting provider, the auto-update hijacked issue is fixed.
Furthermore, even though the v8.8.8 did not fully address the issue, it’s safe due to its “partial” fix according the hijacking schema, if you use auto-updater:
Security enhancement: prevent Notepad++ Updater from being hijacked.Of course, it’s better to update manually to v8.9.1 so you won’t worry about auto-updating in the future.
-
@xomx said in autoupdater and connection temp.sh:
the investigation is still ongoing and @donho will surely disclose more whenever/if it’ll be possible to do so.
Unfortunatly, the investigation actually concluded the day of the announcement (just after the announcement). As I mentioned at the bottom of my announce Edit (February 2, 2026), the IR team was unable to determine the hijacking method, :
Our IR team spent a week analyzing roughly 400 GB of server logs provided by the former hosting provider. While signs of an intrusion were identified, no concrete indicators of compromise - such as binary hashes, domains, or IP addresses - were found. -
@donho Thank you, I did just that (manual update). My older install turned out to be fine as well, thanks to the brilliant strategy of apparently having clicked no to the update prompt for the past 6 years… :)
-
@donho, so if I’ve already auto-updated from 8.8.8 to 8.9.1, would it be necessary or advised to run it again, manually?
-
so if I’ve already auto-updated from 8.8.8 to 8.9.1, would it be necessary or advised to run it again, manually?
Once you have v8.9.1 installed, it won’t be necessary to update your Notepad++ manually - you can just let auto-updater do its job.
-
P PeterJones referenced this topic on
-
P PeterJones referenced this topic on
-
P PeterJones referenced this topic on
-
P PeterJones referenced this topic on
-
P PeterJones referenced this topic on
Hello! It looks like you're interested in this conversation, but you don't have an account yet.
Getting fed up of having to scroll through the same posts each visit? When you register for an account, you'll always come back to exactly where you were before, and choose to be notified of new replies (either via email, or push notification). You'll also be able to save bookmarks and upvote posts to show your appreciation to other community members.
With your input, this post could be even better 💗
Register Login